A Delayed Elastic-Net Approach for Performing Adversarial Attacks
Brais Cancela,
Veronica Bolon-Canedo,
Amparo Alonso-Betanzos
Auto-TLDR; Robustness of ImageNet Pretrained Models against Adversarial Attacks
Similar papers
Optimal Transport As a Defense against Adversarial Attacks
Quentin Bouniot, Romaric Audigier, Angélique Loesch

Auto-TLDR; Sinkhorn Adversarial Training with Optimal Transport Theory
Abstract Slides Poster Similar
Accuracy-Perturbation Curves for Evaluation of Adversarial Attack and Defence Methods
Auto-TLDR; Accuracy-perturbation Curve for Robustness Evaluation of Adversarial Examples
Abstract Slides Poster Similar
Adaptive Noise Injection for Training Stochastic Student Networks from Deterministic Teachers
Yi Xiang Marcus Tan, Yuval Elovici, Alexander Binder
Auto-TLDR; Adaptive Stochastic Networks for Adversarial Attacks
Beyond Cross-Entropy: Learning Highly Separable Feature Distributions for Robust and Accurate Classification
Arslan Ali, Andrea Migliorati, Tiziano Bianchi, Enrico Magli
Auto-TLDR; Gaussian class-conditional simplex loss for adversarial robust multiclass classifiers
Abstract Slides Poster Similar
Attack Agnostic Adversarial Defense via Visual Imperceptible Bound
Saheb Chhabra, Akshay Agarwal, Richa Singh, Mayank Vatsa
Auto-TLDR; Robust Adversarial Defense with Visual Imperceptible Bound
Abstract Slides Poster Similar
Adversarially Training for Audio Classifiers
Raymel Alfonso Sallo, Mohammad Esmaeilpour, Patrick Cardinal
Auto-TLDR; Adversarially Training for Robust Neural Networks against Adversarial Attacks
Abstract Slides Poster Similar
Can Data Placement Be Effective for Neural Networks Classification Tasks? Introducing the Orthogonal Loss
Brais Cancela, Veronica Bolon-Canedo, Amparo Alonso-Betanzos
Auto-TLDR; Spatial Placement for Neural Network Training Loss Functions
Abstract Slides Poster Similar
Defense Mechanism against Adversarial Attacks Using Density-Based Representation of Images
Yen-Ting Huang, Wen-Hung Liao, Chen-Wei Huang
Auto-TLDR; Adversarial Attacks Reduction Using Input Recharacterization
Abstract Slides Poster Similar
Variational Inference with Latent Space Quantization for Adversarial Resilience
Vinay Kyatham, Deepak Mishra, Prathosh A.P.
Auto-TLDR; A Generalized Defense Mechanism for Adversarial Attacks on Data Manifolds
Abstract Slides Poster Similar
Verifying the Causes of Adversarial Examples
Honglin Li, Yifei Fan, Frieder Ganz, Tony Yezzi, Payam Barnaghi
Auto-TLDR; Exploring the Causes of Adversarial Examples in Neural Networks
Abstract Slides Poster Similar
AdvHat: Real-World Adversarial Attack on ArcFace Face ID System
Stepan Komkov, Aleksandr Petiushko
Auto-TLDR; Adversarial Sticker Attack on ArcFace in Shooting Conditions
Abstract Slides Poster Similar
F-Mixup: Attack CNNs from Fourier Perspective
Xiu-Chuan Li, Xu-Yao Zhang, Fei Yin, Cheng-Lin Liu
Auto-TLDR; F-Mixup: A novel black-box attack in frequency domain for deep neural networks
Abstract Slides Poster Similar
Attack-Agnostic Adversarial Detection on Medical Data Using Explainable Machine Learning
Matthew Watson, Noura Al Moubayed
Auto-TLDR; Explainability-based Detection of Adversarial Samples on EHR and Chest X-Ray Data
Abstract Slides Poster Similar
On-Manifold Adversarial Data Augmentation Improves Uncertainty Calibration
Kanil Patel, William Beluch, Dan Zhang, Michael Pfeiffer, Bin Yang
Auto-TLDR; On-Manifold Adversarial Data Augmentation for Uncertainty Estimation
Task-based Focal Loss for Adversarially Robust Meta-Learning
Yufan Hou, Lixin Zou, Weidong Liu

Auto-TLDR; Task-based Adversarial Focal Loss for Few-shot Meta-Learner
Abstract Slides Poster Similar
Knowledge Distillation Beyond Model Compression
Fahad Sarfraz, Elahe Arani, Bahram Zonooz
Auto-TLDR; Knowledge Distillation from Teacher to Student
Abstract Slides Poster Similar
Explain2Attack: Text Adversarial Attacks via Cross-Domain Interpretability
Mahmoud Hossam, Le Trung, He Zhao, Dinh Phung
Auto-TLDR; Transfer2Attack: A Black-box Adversarial Attack on Text Classification
Abstract Slides Poster Similar
Cost-Effective Adversarial Attacks against Scene Text Recognition
Mingkun Yang, Haitian Zheng, Xiang Bai, Jiebo Luo
Auto-TLDR; Adversarial Attacks on Scene Text Recognition
Abstract Slides Poster Similar
Transferable Adversarial Attacks for Deep Scene Text Detection
Shudeng Wu, Tao Dai, Guanghao Meng, Bin Chen, Jian Lu, Shutao Xia
Auto-TLDR; Robustness of DNN-based STD methods against Adversarial Attacks
Killing Four Birds with One Gaussian Process: The Relation between Different Test-Time Attacks
Kathrin Grosse, Michael Thomas Smith, Michael Backes
Auto-TLDR; Security of Gaussian Process Classifiers against Attack Algorithms
Abstract Slides Poster Similar
Removing Backdoor-Based Watermarks in Neural Networks with Limited Data
Xuankai Liu, Fengting Li, Bihan Wen, Qi Li
Auto-TLDR; WILD: A backdoor-based watermark removal framework using limited data
Abstract Slides Poster Similar
Iterative Label Improvement: Robust Training by Confidence Based Filtering and Dataset Partitioning
Christian Haase-Schütz, Rainer Stal, Heinz Hertlein, Bernhard Sick

Auto-TLDR; Meta Training and Labelling for Unlabelled Data
Abstract Slides Poster Similar
Confidence Calibration for Deep Renal Biopsy Immunofluorescence Image Classification
Federico Pollastri, Juan Maroñas, Federico Bolelli, Giulia Ligabue, Roberto Paredes, Riccardo Magistroni, Costantino Grana
Auto-TLDR; A Probabilistic Convolutional Neural Network for Immunofluorescence Classification in Renal Biopsy
Abstract Slides Poster Similar
How Does DCNN Make Decisions?
Yi Lin, Namin Wang, Xiaoqing Ma, Ziwei Li, Gang Bai
Auto-TLDR; Exploring Deep Convolutional Neural Network's Decision-Making Interpretability
Abstract Slides Poster Similar
Polynomial Universal Adversarial Perturbations for Person Re-Identification
Wenjie Ding, Xing Wei, Rongrong Ji, Xiaopeng Hong, Yihong Gong
Auto-TLDR; Polynomial Universal Adversarial Perturbation for Re-identification Methods
Abstract Slides Poster Similar
Adaptive Distillation for Decentralized Learning from Heterogeneous Clients
Jiaxin Ma, Ryo Yonetani, Zahid Iqbal
Auto-TLDR; Decentralized Learning via Adaptive Distillation
Abstract Slides Poster Similar
Knowledge Distillation with a Precise Teacher and Prediction with Abstention
Auto-TLDR; Knowledge Distillation using Deep gambler loss and selective classification framework
Abstract Slides Poster Similar
MINT: Deep Network Compression Via Mutual Information-Based Neuron Trimming
Madan Ravi Ganesh, Jason Corso, Salimeh Yasaei Sekeh
Auto-TLDR; Mutual Information-based Neuron Trimming for Deep Compression via Pruning
Abstract Slides Poster Similar
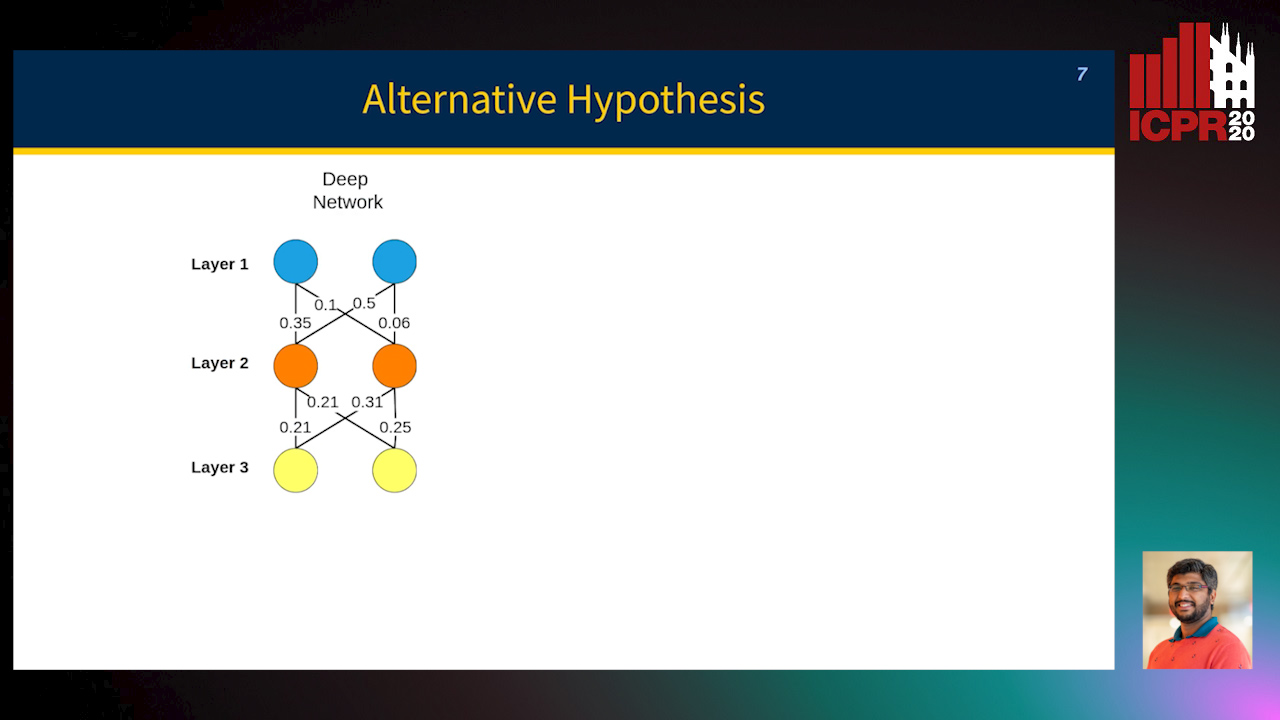
Towards Explaining Adversarial Examples Phenomenon in Artificial Neural Networks
Ramin Barati, Reza Safabakhsh, Mohammad Rahmati
Auto-TLDR; Convolutional Neural Networks and Adversarial Training from the Perspective of convergence
Abstract Slides Poster Similar
Contextual Classification Using Self-Supervised Auxiliary Models for Deep Neural Networks
Sebastian Palacio, Philipp Engler, Jörn Hees, Andreas Dengel
Auto-TLDR; Self-Supervised Autogenous Learning for Deep Neural Networks
Abstract Slides Poster Similar
Nearest Neighbor Classification Based on Activation Space of Convolutional Neural Network
Xinbo Ju, Shuo Shao, Huan Long, Weizhe Wang
Auto-TLDR; Convolutional Neural Network with Convex Hull Based Classifier
Generating Private Data Surrogates for Vision Related Tasks
Ryan Webster, Julien Rabin, Loic Simon, Frederic Jurie
Auto-TLDR; Generative Adversarial Networks for Membership Inference Attacks
Abstract Slides Poster Similar
CCA: Exploring the Possibility of Contextual Camouflage Attack on Object Detection
Shengnan Hu, Yang Zhang, Sumit Laha, Ankit Sharma, Hassan Foroosh
Auto-TLDR; Contextual camouflage attack for object detection
Abstract Slides Poster Similar
Delving in the Loss Landscape to Embed Robust Watermarks into Neural Networks
Enzo Tartaglione, Marco Grangetto, Davide Cavagnino, Marco Botta
Auto-TLDR; Watermark Aware Training of Neural Networks
Abstract Slides Poster Similar
Boundary Optimised Samples Training for Detecting Out-Of-Distribution Images
Luca Marson, Vladimir Li, Atsuto Maki
Auto-TLDR; Boundary Optimised Samples for Out-of-Distribution Input Detection in Deep Convolutional Networks
Abstract Slides Poster Similar
Learning with Multiplicative Perturbations

Auto-TLDR; XAT and xVAT: A Multiplicative Adversarial Training Algorithm for Robust DNN Training
Abstract Slides Poster Similar
Generalization Comparison of Deep Neural Networks Via Output Sensitivity
Mahsa Forouzesh, Farnood Salehi, Patrick Thiran
Auto-TLDR; Generalization of Deep Neural Networks using Sensitivity
Probability Guided Maxout
Claudio Ferrari, Stefano Berretti, Alberto Del Bimbo
Auto-TLDR; Probability Guided Maxout for CNN Training
Abstract Slides Poster Similar
Leveraging Quadratic Spherical Mutual Information Hashing for Fast Image Retrieval
Nikolaos Passalis, Anastasios Tefas
Auto-TLDR; Quadratic Mutual Information for Large-Scale Hashing and Information Retrieval
Abstract Slides Poster Similar
Norm Loss: An Efficient yet Effective Regularization Method for Deep Neural Networks
Theodoros Georgiou, Sebastian Schmitt, Thomas Baeck, Wei Chen, Michael Lew
Auto-TLDR; Weight Soft-Regularization with Oblique Manifold for Convolutional Neural Network Training
Abstract Slides Poster Similar
On the Robustness of 3D Human Pose Estimation
Zerui Chen, Yan Huang, Liang Wang
Auto-TLDR; Robustness of 3D Human Pose Estimation Methods to Adversarial Attacks
Efficient Online Subclass Knowledge Distillation for Image Classification
Maria Tzelepi, Nikolaos Passalis, Anastasios Tefas
Auto-TLDR; OSKD: Online Subclass Knowledge Distillation
Abstract Slides Poster Similar
A Joint Representation Learning and Feature Modeling Approach for One-Class Recognition
Pramuditha Perera, Vishal Patel
Auto-TLDR; Combining Generative Features and One-Class Classification for Effective One-class Recognition
Abstract Slides Poster Similar
Smart Inference for Multidigit Convolutional Neural Network Based Barcode Decoding
Duy-Thao Do, Tolcha Yalew, Tae Joon Jun, Daeyoung Kim
Auto-TLDR; Smart Inference for Barcode Decoding using Deep Convolutional Neural Network
Abstract Slides Poster Similar
Understanding Integrated Gradients with SmoothTaylor for Deep Neural Network Attribution
Gary Shing Wee Goh, Sebastian Lapuschkin, Leander Weber, Wojciech Samek, Alexander Binder
Auto-TLDR; SmoothGrad: bridging Integrated Gradients and SmoothGrad from the Taylor's theorem perspective
A Discriminant Information Approach to Deep Neural Network Pruning
Auto-TLDR; Channel Pruning Using Discriminant Information and Reinforcement Learning
Abstract Slides Poster Similar
Learning Natural Thresholds for Image Ranking
Somayeh Keshavarz, Quang Nhat Tran, Richard Souvenir

Auto-TLDR; Image Representation Learning and Label Discretization for Natural Image Ranking
Abstract Slides Poster Similar
Enlarging Discriminative Power by Adding an Extra Class in Unsupervised Domain Adaptation
Hai Tran, Sumyeong Ahn, Taeyoung Lee, Yung Yi
Auto-TLDR; Unsupervised Domain Adaptation using Artificial Classes
Abstract Slides Poster Similar